Default 2FA enabled by 23andMe data theft
DNA testing and genealogy companies are making sure their users’ accounts are more secure by requiring them to use two-factor authentication. This comes after the theft of millions of user records from the big DNA testing company 23andMe.
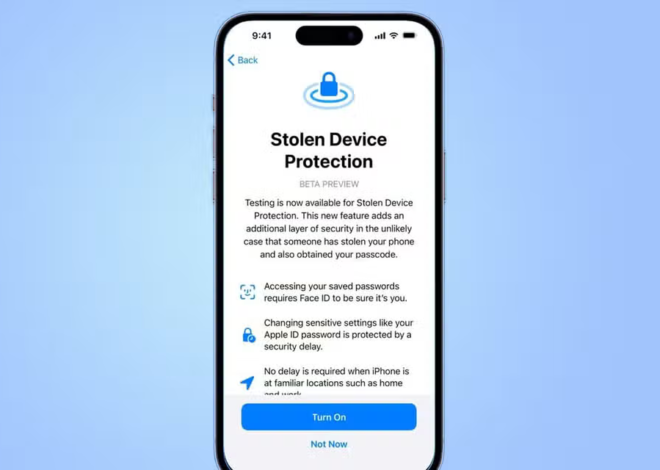
Ancestry, MyHeritage, and 23andMe are letting their customers know that they will now use a security feature called two-factor authentication (2FA) by default. With 2FA, when users log in, they will need to enter an extra verification code that is sent to a device they own. This is done to make sure that the person logging in is the real account owner.
Ancestry has sent emails to its customers, informing them that they will need to use “two-step verification” to sign in. This means they will receive a code on their phone or email, and they must use it to log into their account. AncestryDNA customers who want to see their DNA matches will be required to use this multi-factor authentication by the end of the year.
MyHeritage recently announced in a blog post that they will soon make two-factor authentication (2FA) a mandatory requirement for their DNA customers, citing the data breach at 23andMe. Similarly, 23andMe also stated that they are now requiring all their customers to use a second verification step to sign into their accounts.
Together, Ancestry, MyHeritage, and 23andMe have over 100 million users.
This decision to implement 2FA as the default security measure comes after 23andMe disclosed in October that they were investigating a data breach where a hacker claimed to have stolen millions of 23andMe account records, including one million users of Jewish Ashkenazi descent and 100,000 Chinese users.
23andMe explained in a blog post at that time that they believed the hackers gained access to 23andMe user accounts by using stolen usernames and passwords that had been exposed in previous data breaches. The hackers collected profile and genetic data from 23andMe users who had opted into the DNA Relatives feature, which allows users to automatically share their data with others who use the feature.
TheOrcTech discovered that some of the stolen data had been advertised as early as August and included known and publicly available 23andMe user and genetic information.
Also Read | GitHub launches passkey support into general availability (GitHub PassKey)
Genetics and genealogy companies have been attractive targets for cyberattacks and data theft due to the valuable and sensitive personal and genetic data they store. For instance, in 2020, the DNA analysis website GEDmatch reported two data breaches that exposed user data.
Also Read | 23andMe confirms stolen user data
In 2019, the DNA testing company Veritas Genetics also fell victim to a data breach that resulted in the compromise of customer information. These incidents highlight the ongoing security challenges faced by companies in this industry.